2019-01-16 - Exploit Integration
CVE-2018-15982 (Flash Player up to 31.0.0.153) and Exploit Kits
The CVE-2018-15982 is a bug that allows remote code execution in Flash Player up to 31.0.0.153, spotted in the wild as a 0day. Patched on December 05, 2018 with APSB18-42.
Underminer:
Underminer exploit kit improves in its latest iteration - 2018-12-21 - Malwarebytes
Fallout:
2019-01-16
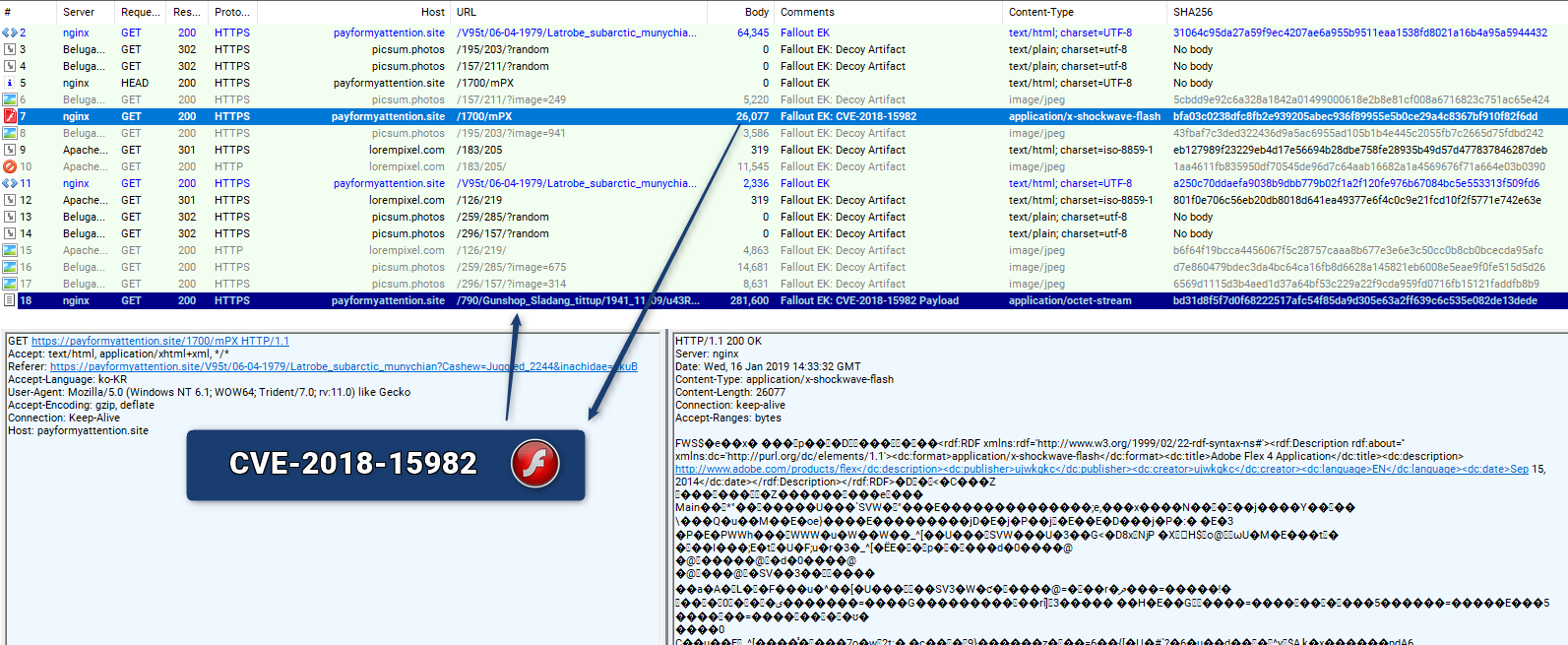
Files: Fiddler on VT - Pcap on VT
Associated Advert underground:
Итак! Тяжкие работы по восстановлению всей инфраструктуры связки закончены, были проведены тесты и в данный момент связка работает в полном объеме. Также были произведены множество правок и изменений.
Изменения:
- Увеличена производительность
- Полностью переработан механизм обфускации кода и генерации лэндинга.
- Убран CVE-2018-8373 на переработку. В данный момент сплоит ведет себя не стабильно.
- Добавлен новый флеш сплоит CVE-2018-15982.
- Для запуска повершелл в шеллкод добавлен код отключения AMSI
- Кучка мелких правок
ИЗМЕНЕНА ЦЕНОВАЯ ПОЛИТИКА Неделя 400$ Месяц 1300$
В данный момент при проверке отстука софта со связки было выявлено:
- Отстук EXE на уровне 80-90%
- Отстук PowerShell на уровне 95-100%
Translated by google as:
So! The hard work on the restoration of the entire infrastructure of the bundle was completed, tests were carried out and at the moment the bundle is working in full. There have also been many edits and changes.
Changes:
- Increased performance
- The code obfuscation and landing generation mechanism has been completely redesigned.
- Removed CVE-2018-8373 for recycling. At the moment, the flow rate is not stable.
- Added new flash sploit CVE-2018-15982.
- To launch Powershell, the disable code AMSI is added to the shellcode
- A bunch of minor edits
CHANGED PRICE POLICY Week 400 $ Month $ 1300
At the moment, when checking the otstuk software from the bundle, it was revealed:
- Otstuk EXE level 80-90%
- Otstuk PowerShell at the level of 95-100%
| IOC | Type | Comment | Date |
|---|---|---|---|
| payformyattention[.]site|51.15.35[.]154 | domain|IP | Fallout EK | 2019-01-16 |
| whereismyteam[.]press|51.15.111[.]159 | domain|IP | Fallout EK | 2019-01-16 |
| bd31d8f5f7d0f68222517afc54f85da9d305e63a2ff639c6c535e082de13dede | SHA-256 | GandCrab Ransomware | 2019-01-16 |
Spelevo:
2019-03-06 Appears to be a new Exploit Kit which has some similarities with “SPL EK”. (CVE-2018-8174 has been spotted there as well)
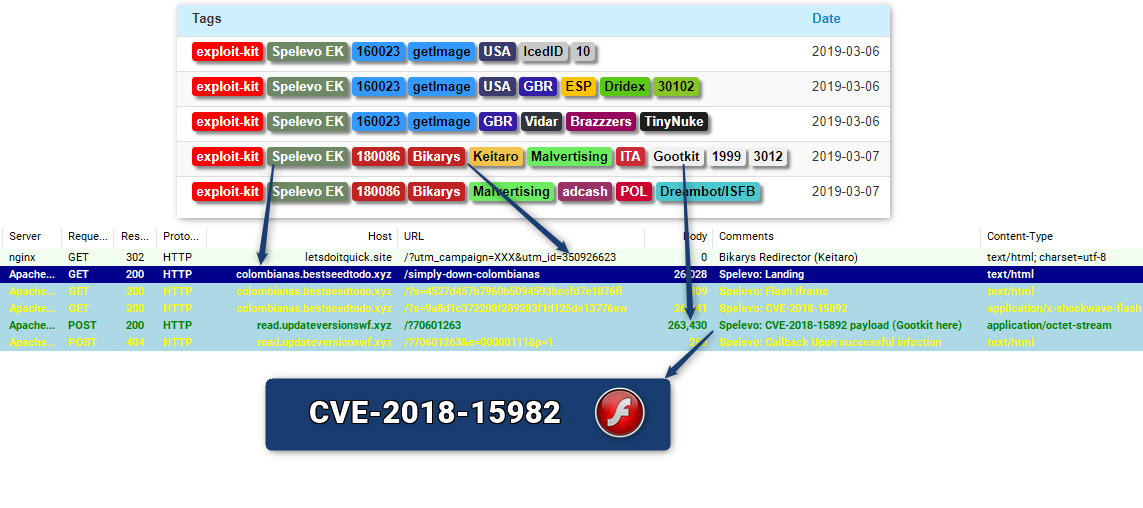
Acknowledgement:
Thanks to Chaoying Liu for CVE confirmation.
Files: Fiddler on VT - Pcap on VT (note: Some proxy were used)
| IOC | Type | Comment | Date |
|---|---|---|---|
| letsdoitquick[.]site|194.113.107.71 | domain|IP | Redirector (Keitaro TDS) | 2019-03-07 |
| index.microsoft-ticket[.]xyz|85.17.197[.]101 | domain|IP | Spelevo EK | 2019-03-06 |
| blasian.bestseedtodo[.]xyz|85.17.197[.]101 | domain|IP | Spelevo EK | 2019-03-06 |
| flashticket[.]xyz|85.17.197[.]101 | domain|IP | Spelevo EK | 2019-03-06 |
| read.updateversionswf[.]xyz|85.17.197[.]101 | domain|IP | Spelevo EK | 2019-03-07 |
| 9aa8e341cc895350addaf268b21f7a716f6d7993575fdba67a3fe7a9e23b8f90 | SHA-256 | Gootkit “1999” | 2019-03-07 |
| 2feba3cc47b7f1d47a9e1277c4f4ad5aa5126e59798ac096459d1eae8f573c35 | SHA-256 | Gootkit “3012” (2nd Stage) | 2019-03-07 |
| ws.blueberryconstruction[.]it|185.158.250[.]163 | domain|IP | Gootkit C2 | 2019-03-07 |
| ws.diminishedvaluevirginia[.]com|185.158.251[.]115 | domain|IP | Gootkit C2 | 2019-03-07 |
| gttopr[.]space|198.251.83[.]27 | domain|IP | Gootkit C2 | 2019-03-07 |
19.03.26 #Malvertising -> #GreenFlashSundown EK-> #SeonRansomware ver 0.2 & #pony & #miner using CVE-2018-15982 - 2019-04-05 - @vigilantbeluga
Shadowgate Returns to Worldwide Operations With Evolved Greenflash Sundown Exploit Kit - 2019-06-27 - Trendmicro
Read More:
Adobe Flash Zero-Day Exploited In the Wild - 2018-12-05 - Gigamon
Underminer exploit kit improves in its latest iteration - 2018-12-21 - Malwarebytes