2013-02-21 - Geo-Focus
CBeplay.P : Now target Australia and moved to server side localization
.png) |
CBeplay is stealing/borrowing design from Urausy (AU - ES - NL)
- It's not talking anymore to UK Citizen
- The design is not embedded anymore in the binary but downloaded from the C&C.
(to be honest I was expecting that move to occur earlier, this choice was complicating their life for sure. This required one exploit kit landing by binary (on Cool EK) and traff work in front of the exploit kit + more compilation/crypting)
This move allow the team to enjoy font drop with one fixed payload and to easily target more countries.
Expect far more to come.....
All Design :
(a small watermark has been included, up left, on some - sorry about that, too lazy to remake affected screenshots)
Australia (newly targeted by this threat - it's also the Default design) :
 |
| CBeplay.P AU in it's Windows Form - 2013-02 |
.png) |
| CBeplay.P AU (scroll inside the form) 2013-02 |
Austria (updated design):
 |
| CBeplay.P AT 2013-02 in its Windows form |
 |
| CBeplay AT 2013-02 Scrolled |
Belgium (no change) :
 |
| CBeplay.P BE 2013-02 |
France (no change but new capture for me) :
 |
| CBeplay.P FR |
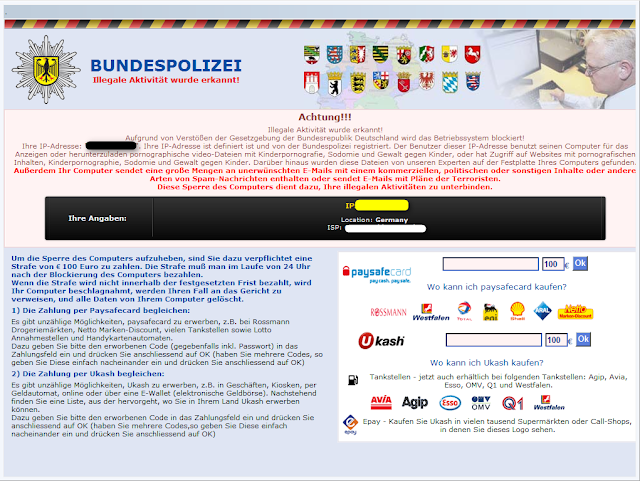 |
| CBeplay.P DE 2013-02 |
 |
| CBeplay.P IT 2013-02 |
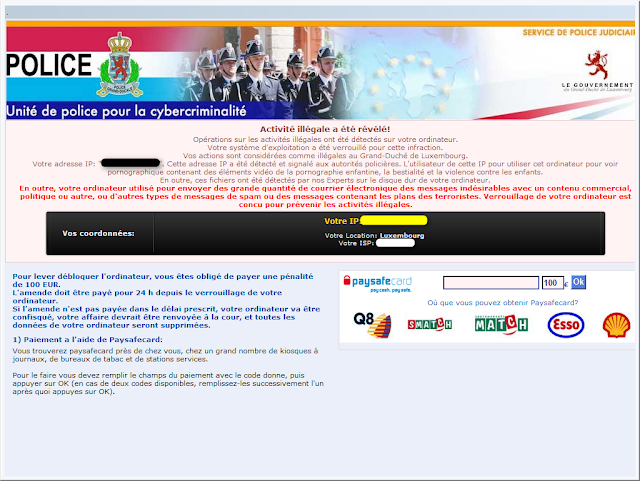 |
| CBeplay.P LU (2013-02) |
Netherlands (no change):
 |
| CBeplay NL 2013-02 |
Spain (updated design) :
 |
| CBeplay.P ES in its windows Form (2013-02) |
.png) |
| CBeplay.P ES Scrolled 2013-02 |
 |
| CBeplay.P SE 2013-02 |
United Kingdom (no more voice):
 |
| CBeplay.P UK 2013-02 |
 |
| CBeplay.P US 2013-02 |
C&C :
Design : 87.117.253.11
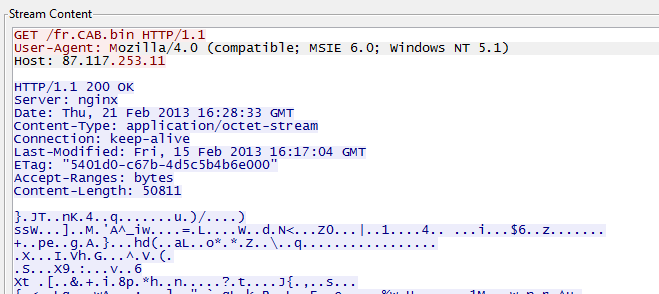.png) |
| French Design download by CBeplay.P |
1.png) |
| "Mama's gonna make all your nightmares come true." |
(Got some help on that one. Waiting approval for proper credits)
 |
| Cool EK CVE-2013-0431 successfull path leading to infection by CBeplay.P |
883cfd95ccc89de70c20015e8479e936_CBeplay.P_210213.zip (Mega via Goo.g shortener)
883cfd95ccc89de70c20015e8479e936_CBeplay.P_210213.zip (OwnCloud via Goo.gl shortener)
Read:
Botnets.fr CBeplay.P page
Don’t Pay Up – How To Beat Ransomware! - 2013-04-05 - MakeUsOf - Guy McDowell
